Cloud Data Masking and Privacy Protection: Using Production Data Safely in Dev/Test Environments
Last year, a client was fined by a regulator. A test environment had leaked thousands of customer phone numbers. The investigation found that a developer had copied the production database to the test environment without any masking. The test database was then compromised. The numbers were real.
The technical lead said: “But we encrypted everything.”
They encrypted the production database. The test database was plain text.
This is the blind spot of data security: production is locked down, but dev/test is wide open.
Today, let’s talk about data masking and privacy protection. Not the “encrypt your data” fluff, but a practical guide: how to safely use production data in development and test environments, static vs dynamic masking, and how to keep data useful while protecting privacy.
01 Using Raw Production Data in Dev/Test Is a High‑Risk Operation
Many teams copy the production database to test environments because “it’s real data – bugs reproduce accurately.”
But test environments have far weaker security than production. Fewer access controls. No audit logs. Sometimes even exposed to the public internet.
According to a 2024 security report, over 40% of data breaches involve non‑production environments – and test environments lead the list.
Counter‑intuitive truth: test environments are often riskier than production itself.
That client locked down production with encryption, audit logs, and strict IAM. The test environment had none of that. Attackers didn’t break into production. They broke into the test copy and got the same real data.
02 Masking Is Not Encryption
Many people confuse masking with encryption. They are different.
Encryption is reversible. With the key, you get the original data. Good for storage and transmission.
Masking is irreversible or very hard to reverse. It preserves format and business rules but removes personal identifiability.
Example: phone number 13812345678
Encryption → ciphertext (reversible)
Masking →
138****5678or a random but valid number13888888888
The principle of masking: keep usability, remove identifiability.
Dev and test need data that obeys business rules (phone numbers have 11 digits, ID numbers follow a checksum).
They do not need the real phone number or ID.
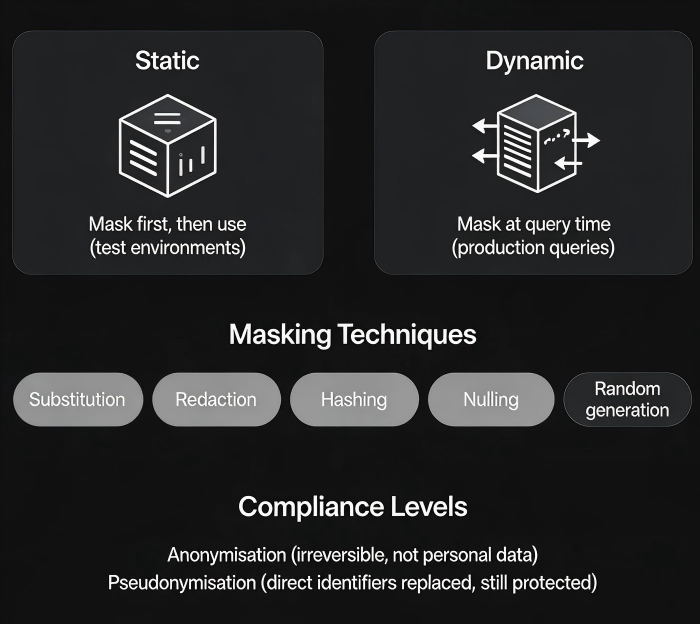
03 Static Masking vs Dynamic Masking
Two mainstream approaches for different scenarios.
Static masking (SDM): mask first, then use
Flow: production → masking engine → masked test database → dev/test teams
Pros:
One‑time process; no runtime overhead after masking
Suitable for large datasets moved to test environments
Cons:
Masked data is static; it doesn’t reflect real‑time production changes
Requires additional storage
Dynamic masking (DDM): mask at query time
Flow: application/tool queries → masking gateway intercepts → real‑time masking → masked results
Pros:
No duplicate data; saves storage
Always reflects current production data
Cons:
Overhead per query; impacts performance
Not suitable for offline batch processing
The client adopted static masking. On export from production, fields like phone number, ID number, and name were automatically masked before being loaded into the test database. Developers saw data that looked real but could not be linked to real individuals.
04 Common Masking Techniques
Different data types require different techniques.
Substitution: Replace real values with fake ones from a dictionary. Name → random name, address → random address. Maintain cross‑table consistency (same person gets the same fake name across tables).
Redaction / masking: Partially hide characters. Phone
138****5678, ID1101**********1234. Good for display scenarios.Hashing: Irreversible, but the same input produces the same output. Useful for join keys when the raw value is not needed.
Nulling out: Set to NULL. Suitable for fields that are not required.
Random generation: Generate random but format‑compliant values. Phone numbers must be 11 digits and follow valid carrier prefixes.
Subsetting: Take only a portion of the data instead of the whole dataset. Reduces the exposure surface.
05 Compliance: GDPR and PIPL
Both GDPR and China’s Personal Information Protection Law (PIPL) require de‑identification of personal data in non‑production environments.
Anonymisation: Data can no longer be linked to an individual, and the process is irreversible. Anonymised data is not considered personal data and can be freely used.
Pseudonymisation: Direct identifiers (name, ID number) are replaced with pseudonyms. The data is still considered personal data and requires protection.
For dev/test environments, pseudonymisation is the typical choice. It keeps the data usable for testing while removing obvious identifiers.
Compliance key points:
Document the purpose of data usage
Apply the data minimisation principle (only necessary fields)
Masked data still needs access controls
Keep logs of masking operations
06 A Real Story
A financial company used real credit card numbers in their test environment. Although they kept only the first six and last four digits, those partial numbers could still be used to deduce the full card.
They implemented three changes:
Deployed a data masking platform with automatic sensitive data discovery.
Added a static masking step in the pipeline between production and test environments.
Credit card numbers: replaced with randomly generated test numbers that passed the Luhn checksum.
Names and addresses: replaced with random values while maintaining referential integrity across tables.
Configured dynamic masking for production queries: sensitive fields were automatically redacted at query time.
Their security lead said: “The test environment used to feel like a risk warehouse. Now we can safely share it with external contractors.”
The Bottom Line
Data masking is the practice of balancing usability and privacy.
That client’s ops lead later said: “You can build a high wall around production. But if the test environment is open, the wall means nothing. Masking isn’t an extra cost – it’s basic data governance.”
Is your test environment still using raw production data?

