Cloud Ops Automation Toolchain: Terraform, Ansible, Helm, ArgoCD – How to Choose and Integrate
Last year, a client asked me: “We want to automate everything. I’ve heard of Terraform, Ansible, Prometheus, Helm, ArgoCD. I don’t know which one to start with. Do I need all of them? Is Ansible outdated if I use Kubernetes?”
This is the confusion many teams face. Too many tools. No clear answer on what does what or how they fit together.
Today, let’s talk about the cloud ops automation toolchain. Not the “every tool is important” fluff, but a practical guide: what each tool solves, how they work together, and which one to start with.
01 More Tools Is Not Better
Many teams try to adopt every tool at once. That’s a mistake. A toolchain is about integration, not collection. Too many tools create fragmentation. Teams can’t learn them all. Maintenance costs climb.
The right approach: start from pain points. Add tools one at a time.
The client’s pain points:
Servers created manually, configurations inconsistent
Deployments done by hand – many steps, frequent errors
Configuration drift after launch – no one knew who changed what
We built a toolchain step by step, from infrastructure to application deployment.
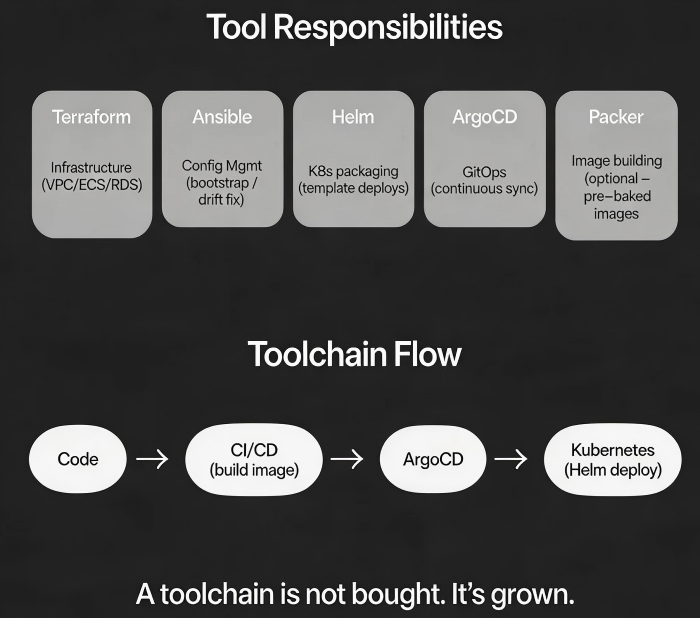
02 Tool Responsibilities: Each Owns a Layer
Let’s look at what each tool actually does.
Terraform: Infrastructure as Code
Owns cloud resources: VPC, subnets, EC2, RDS, load balancers, security groups.
Declarative: write code describing what you want, Terraform creates it
Cloud‑facing, not server‑internal
Manages lifecycle of cloud resources
Ansible: Configuration Management
Owns what happens inside servers: installing software, editing config files, creating users, setting kernel parameters.
Agentless – runs over SSH
Idempotent – same result no matter how many times you run it
Good for server bootstrap and fixing configuration drift
Packer: Image Building (optional)
Owns custom images with pre‑installed software. Build once, use many times.
Speeds up scaling – new instances are ready immediately
Great for large auto‑scaling fleets
Helm: Kubernetes Application Packaging
Owns how applications are packaged for Kubernetes. Turns many YAML files into a single, parameterized chart.
Template‑based – one chart for dev, staging, production
Version management – easy upgrades and rollbacks
Tailored for Kubernetes
ArgoCD: GitOps Continuous Delivery
Owns continuous synchronization of Kubernetes applications. The Git repo is the source of truth. ArgoCD keeps the cluster state identical to what’s in Git.
Declarative: desired state in Git, ArgoCD makes it reality
Fixes drift automatically – manual changes are reverted
Good for multi‑cluster GitOps workflows
03 The Toolchain Flow
Here’s how the tools typically connect:
text
Git → CI/CD (build image) → Registry → ArgoCD (sync) → Kubernetes ↑ └── Helm (package app) Cloud layer: Terraform (VPC, ECS, RDS, EKS) Config layer: Ansible (bootstrap, install agents, set kernel params) Image layer: Packer (pre‑built images – optional)
That client adopted tools stepwise:
Phase 1: Terraform for cloud resources. No more clicking in the console. Everything in code, auditable and rollback‑able.
Phase 2: Ansible for instance bootstrap. New instances automatically installed agents, configured monitoring, and joined the cluster.
Phase 3: Helm for Kubernetes deployments. The same chart served dev, staging, and production with different value files.
Phase 4: ArgoCD for GitOps. A PR merged in Git triggered ArgoCD to sync the cluster. No more manual kubectl apply.
04 Not Every Tool Is Required
The toolchain is not a fixed menu. Choose based on team size and stage.
Small team, few servers – Ansible might be enough. Skip Terraform if you can click a console without losing control.
On Kubernetes but modest scale – Helm + CI/CD may be enough. Add ArgoCD when you have multiple clusters or teams.
Large scale, many environments, multiple teams – Use the full chain. IaC, config management, GitOps – all needed.
That client initially wanted every tool at once. We stopped them. Terraform + Ansible first. When that was stable, add Helm. When Helm matured, add ArgoCD. Each phase stabilized before the next.
05 Common Traps
Trap 1: Using Terraform to manage server‑internal config
Terraform has remote-exec and provisioners, but they’re for emergencies, not daily use. Keep the boundary clear: Terraform for cloud resources, Ansible for server internals.
Trap 2: “K8s means Ansible is dead”
Kubernetes nodes themselves still need bootstrap: install Docker, set kernel parameters, mount disks. Ansible handles node preparation. Kubernetes handles applications.
Trap 3: “ArgoCD replaces CI/CD”
ArgoCD only synchronizes. It doesn’t build images. CI/CD builds images and pushes to a registry. ArgoCD deploys them.
Trap 4: “The full toolchain must be deployed before we see value”
No. Start small. Phase 1 might be just a few Jenkins scripts. As you feel the pain, peel off pieces into dedicated tools.
06 A Real Story: From Manual to Full Automation
A client ran 50 servers in a hybrid cloud. No automation. Deployments were manual. Troubleshooting meant digging through phone notes.
We built the toolchain in phases:
Phase 1: Terraform to manage cloud resources. VPC, ECS, RDS – all in code.
Phase 2: Ansible playbooks for server bootstrap. Init, monitoring, logging – about a dozen playbooks.
Phase 3: Packer to build custom images. Base software baked into images – new instances started ready to serve.
Phase 4: GitLab CI + Helm for automated Kubernetes deployments.
Phase 5: ArgoCD for GitOps. Merge PR → automatically synced to production.
One year later, deployment time dropped from hours to minutes. Their ops lead said: “We used to need two people for a deployment. Now I just merge a PR, and ArgoCD handles the rest.”
The Bottom Line
There is no one “right” toolchain. The right toolchain fits your team’s size, pain points, and maturity.
That client’s ops lead later said: “We didn’t buy the whole toolchain at once. We added pieces as they became necessary. Terraform fixed messy cloud resources. Ansible fixed config drift. Helm fixed messy K8s deploys. ArgoCD fixed drift again. Each tool solved one problem.”
Start with your biggest pain point. Is it cloud resource management? Server configuration? Application deployment? Start there. Add tools as you go.
A toolchain is not bought. It’s grown.

